
Enterprise cybersecurity technology research that connects the dots.
The company performed well in all solution capability categories, including analytics, secrets management, privileged delegation and elevation management, and privileged access governance.
When Omdia took a detailed look at privileged access management (PAM) in 2015, the technology was almost entirely available as software for deployment on a customer's premises. That situation has changed in the intervening years, and PAM has followed its more generic big brother, identity and access management (IAM), in migrating to the cloud to be delivered in software-as-a-service (SaaS) mode, at least as a deployment option.
Omdia's purpose through this Universe research is to help technology decision-makers take informed, balanced, and smart decisions so that they can best utilize and benefit from the myriad PAM products that exist. In turn, Omdia wants to help technology vendors further understand their position in the market and how they can better address the needs of users and anticipate the technology disruption of the future.
To best support our objective of guiding technology decision-makers, the report looks at a broad set of solution capabilities offered by nine vendors: CyberArk, Centrify, Krontech, ManageEngine, Remediant, Senhasegura, SSH.COM, Stealthbits, and Thycotic. To garner customer insights, Omdia did a customer survey and partnered with software review site TrustRadius to support and further inform this report and provide relevant insights from customer reviews. Omdia thus creates a balanced and enhanced picture to inform and advise decision-makers about the end-user experience with products from the nine vendors we evaluated. Omdia choose Trust Radius as the most trusted review site for business technology, used by more than 1 million buyers each month and optimized for content quality and data integrity.
The section below provides the ranking for each vendor in our PAM Omdia Universe. There is also a short description why each vendor has been classified based on various categories:
Leaders
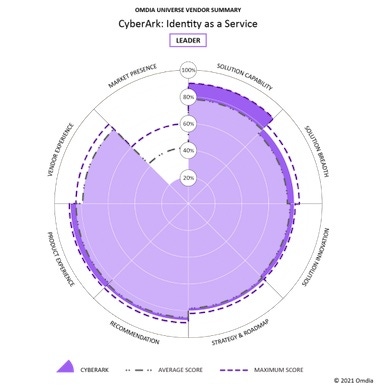
CyberArk is the Market Leader in Privileged Access Management by some considerable margin, with reported revenue for 2020 just shy of half a billion dollars, and most of its challengers still quite a lot smaller. The company performed well in all solution capability categories, including analytics, secrets management, privileged delegation and elevation management, and privileged access governance.
Centrify and Thycotic are also ranked as leaders. In April 2021, Centrify and Thycotic, announced their intention to merge, precisely to gain the technical and market clout needed to mount a more serious challenge to the leader.
Senhasegura also ranks as a leader in this report, not because of its revenues, which are smaller than those of CyberArk, Thycotic, and Centrify, but on account of its product capabilities, solution innovation, and customer experience.
Finally, we rank Krontech as a leader here, on account of its strongest subcategories, which were solution capability, solution innovation, customer vendor experience, and product experience.
Challengers
Remediant is ranked as a challenger in this report. The company is good for agentless and vaultless technology. Remediant's strongest categories were vendor experience, customer recommendation, and solution capability.
ManageEngine is also a challenger in this PAM Omdia Universe. ManageEngine has an attractive pricing model that does not charge by user or device. ManageEngine has good customer support and a high customer satisfaction level.
Finally, we rank SSH as a challenger. SSH's PAM product, called PrivX, is lightweight by design, created to perform the core task of access management, with capabilities such as analytics and risk detection deliberately excluded to allow for integration with best-of-breed platforms.
Prospects
Stealthbits, ranks as a Prospect. Stealthbits Privileged Activity Manager currently lacks some features, but they are on the vendor's road map to be added or increased. These include things such as secrets management across native cloud, DevOps, containerized, and other dynamic environments.
Omdia Awards
Hitachi ID Systems should also be on your radar and is one to watch. The vendor has been in the identity management market for nearly three decades, offering a suite of products that consists of products in IAM, PAM, and password management, and a cloud-based version of its IAM platform has been in existence for several years. It has also offered a PAM product since 2005, so it has considerable expertise in this area.
Category Definitions
Market leaders — This category represents the leading solutions that Omdia believes are worthy of a place on most technology short lists. The vendors have established a commanding market position with products that are widely accepted as best of breed.
Market challengers — The solutions in this category have a good market positioning, and the vendors are selling and marketing the product well. The products offer competitive functionality and a good price-performance proposition and should be considered as part of the technology selection.
Market prospects — The solutions in this category are also worthy of inclusion on a short list. They typically provide the core functionality needed but vendors may be a newcomer to the market, specialize in a particular segment, or have a regional focus.
About the Author(s)
You May Also Like
Defending Against Today's Threat Landscape with MDR
April 18, 2024The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024

