In celebration of Black Hat's 20th birthday, we take a look back at the most memorable presentations and demos since the show's inception in 1997.
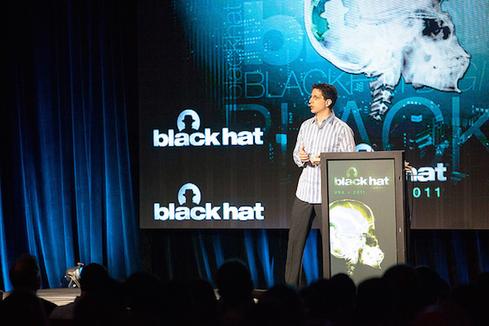
This year marks the 20th anniversary of Black Hat, the information security conference founded by Jeff Moss in 1997. What began as a single meetup in Las Vegas has expanded around the world to host events in the United States, Europe, and Asia.
Over the years, Black Hat has brought together CISOs, researchers, academics, IT specialists, analysts, federal employees, cryptographers, and many other security professionals to learn about, and discuss, the threats and trends shaping their industry.
Much of the learning takes place in the Black Hat Briefings, which were created to give security pros a place to discover new threats and developments that could potentially put them at risk. Each year, researchers take the conference stage to share their latest work and exploits.
Twenty years is a long time in an industry where threats change by the minute. The many vulnerabilities exposed at Black Hat have affected everything from consumer devices to critical infrastructure.
For example, anyone who was at Black Hat 2010 recalls when the late Barnaby Jack, then director of research at IOActive, demonstrated how a cybercriminal could compromise an ATM and steal cash, copy customers' card data, or learn the machines' master passwords.
Information released at Black Hat has proven groundbreaking and game-changing for those in attendance. Here, we take a look back at the "best of" Black Hat talks, discoveries, and moments over the past 20 years.
Do you have a favorite Black Hat moment that didn't make this list? If so, we'd love to hear about it! Feel free to share your thoughts in the comments.
Read more about:
Black Hat NewsAbout the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




