The journey starts with three steps: Engage the C-suite, think like a hacker, and look at the big picture.
As high-profile data breaches make headlines, CIOs and CSOs often stand between the C-suite and the next public IT failure. Some may wonder: Is "scapegoat" now a part of IT's job description?
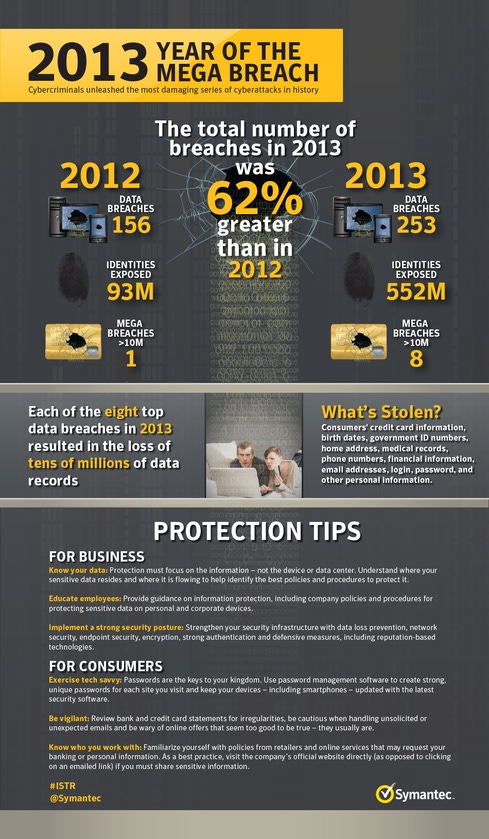
Symantec's Internet Security Threat Report shows a 62% increase in the number of data breaches in 2013 from 2012. Further to that, the number of mega breaches -- a term Symantec uses for breaches that expose more than 10 million identities in a single incident -- went from just one in 2012 to eight in 2013. These massive breaches impact brand reputation, reduce trust, spawn legal and compliance liabilities, and disrupt customer relationships.
No silver bullet
As CIO at Symantec, I'm often asked, "Isn't there some new 'thing' that can prevent these breaches from happening?" Unfortunately, there is no silver bullet. The overwhelming complexity of today's technology makes it unlikely that there could ever be single solution to keep us secure 100% of the time.
Breaches often involve increasingly sophisticated hacker attacks that exploit the weakest links in an organization's security posture -- at the data center, messaging gateway (like email), the endpoint (mobile devices, laptops) or even employees themselves. A company's security, as we have seen with the retirement of Windows XP and the discovery of the Heartbleed bug in OpenSSL, is also inevitably linked to an evolving global information technology ecosystem.
In other words, as our IT landscape changes new risks to our information arise. Although security remains a top priority, IT departments are driving mobile, cloud, big data, and the Internet of Things initiatives that will enable workforce productivity but also present new potential security risks. Effective partnerships between the CIO and CSO are so critical because security is inherently tied to IT's productivity efforts; one cannot come at the expense of the other.
So what's the path forward? Here are three important steps CIOs and CSOs can take to protect their organization's information:
Engage the C-suite
CIOs and CSOs need to proactively counsel their colleagues on the C-suite about information risks and explain in plain language what resources they need to transition from older, vulnerable systems, and partner with the right organizations to identify and protect vulnerabilities in their organization's information supply chain. Engaging the CEO and CFO can help IT get the security resources it needs to be successful, the CMO can help IT understand what data it is obtaining and storing from customers and the CTO can help IT understand the most critical IP it has that deserve the greatest attention to security. Engaging the c-suite is critical to getting out in front of issues like the retirement of Windows XP and developing a company-wide incident response plan in case of a breach or emergency.
Think like a hacker
Hackers are like water, they flow to the path of least resistance. Consider your organization's IT structure from a hacker's vantage point -- where is our most valuable data stored and backed up? Where are the vulnerable points that I could exploit? What offers the greatest ROI for my hacking efforts?
To gain this perspective, consider enlisting the help of partners outside your organization. Facebook recently launched a bounty program to identify vulnerabilities not only on public sites but in their internal infrastructure, so they can patch vulnerabilities before the next hacker finds and exploits them. Also, security vendors keep their eyes open 24/7 for threats and vulnerabilities all over the globe. Maintaining a threat intelligence network requires significant resources that IT departments typically do not have. Partnering with the right experts allows IT to receive the benefits of their threat intelligence infrastructure so they can secure systems far faster and more effectively that they could by themselves (disclosure: Symantec is one of several information security vendors who provide this type of threat intelligence).
Look at the big picture
A multitude of different services in our everyday lives help protect the things we care about. We count on banks to store our money, we hire security services in dangerous times and we insure our most valuable belongings like our homes.
To protect corporate data, a strong global security program will need to include five critical components: Discover, Prevent, Detect, Respond, and Recover. Historically, organizations have been focused on the first two, which largely play a role to prevent an attack. But what we all know now is that successful cybersecurity programs should assume that an incident is not a matter of if, but when, and that these other facets are also critically important. From a Detect, Respond, and Recover perspective, tools like data loss prevention, incident response and implementing a company-wide risk management program, can greatly diminish (or eliminate) potential damage should a successful attack occur -- marking the difference between incident and catastrophe.
Let's not fear our times. IT is much more than a cost center or scapegoat. There may not be a silver bullet to cybersecurity but there are proactive steps we can take to protect our information so we can focus on the things that matter most.
About the Author(s)
You May Also Like
Defending Against Today's Threat Landscape with MDR
April 18, 2024The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




