A benchmarking system would help buyers choose more secure software products and, more importantly, light a fire underneath software producers to make products secure.

Prompted in part by devastating attacks such as those on SolarWinds Orion, Microsoft Exchange, and Colonial Pipeline, the White House issued an executive order on cybersecurity in May. Application security is a prominent part of the document, with special emphasis on software supply chain security for all applications used by the federal government.
The administration's emphasis on software supply chains is welcome considering the current threat environment. SolarWinds customers, for example, had no control over the integrity of that company's software and no way of knowing there would be a problem with a particular software update. SolarWinds Orion was simply off-the-shelf software they had purchased. In fact, affected SolarWinds customers were doing the right thing by installing updates quickly.
A Possible Software Security Scoring System
Although the regulations needed to implement the executive order have not yet been issued, one possible way of benchmarking compliance would be a rating system for software security. The Cyberspace Solarium Commission (CSC), which was formed in 2019 to develop a consensus on a strategic approach to defending the United States against cyberattacks, recommended in its 2020 report a voluntary system — similar to the Energy Star ratings on US appliances and Singapore's rating system for Internet of Things (IoT) devices. Others are pushing to make it mandatory.
Some observers have advocated for a scoring system for software for more than a decade. A public software security label with an easy-to-understand, easy-to-calculate overall score and supporting details is the key. Some consumers will use the label to choose more secure software products, but more importantly, such a labeling scheme will motivate software companies to improve their public scores by investing in robust application security for their products.
What Should a Scoring System Look Like?
While a software scoring system could take different forms, one requisite aspect is the need to take the entire software supply chain into account. Software providers need to know the security ratings of their applications' component parts — the open source libraries that are so ubiquitous in software these days. This is because upwards of 90% of applications contain code from third-party libraries. Once a piece of off-the-shelf software is taken to market, the users of that software need a single, overall security score that accounts for the component parts.
It is infeasible to come up with a perfect instrument to measure every aspect of security for every type of software possible. But it is possible to create a framework that (1) empowers software buyers to make more informed decisions, and (2) encourages producers to build better software with more security visibility.
Below is a conceptual model to help imagine how such a scoring system might work. Software is simply evaluated against six key security areas and assigned a grade. As you can see, things are haphazard or nonexistent at the bottom, while those at the top are continuous, automated, standardized, and comprehensive.
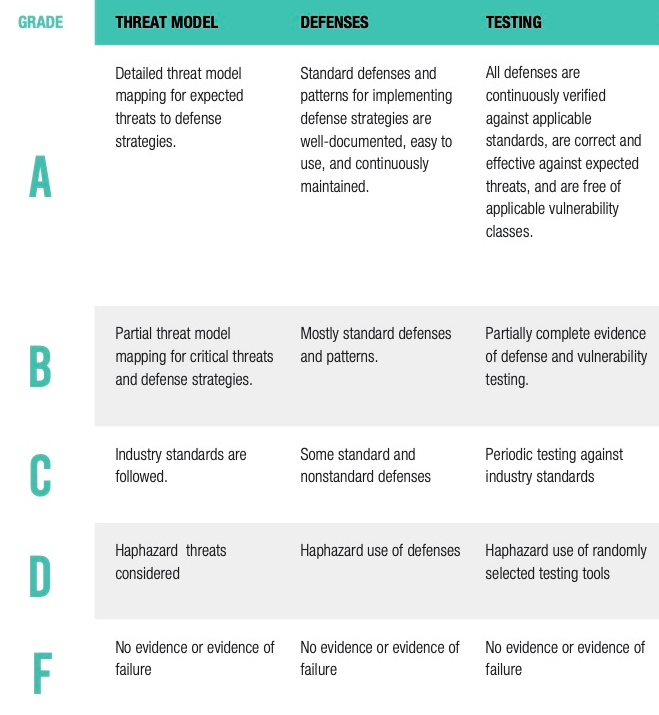
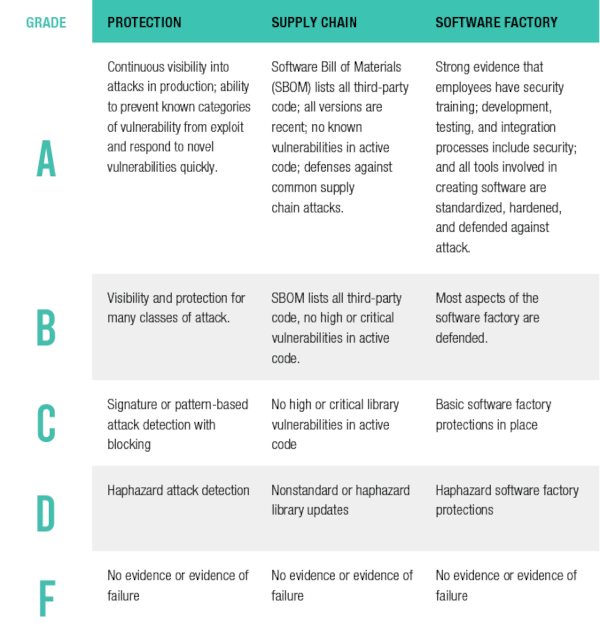
Credit: Contrast Security
Based on an application's score in each of these categories, an overall letter grade could be assigned that would be visible on product webpages, marketing materials, and physical packaging. Based on this easy-to-understand letter grade, organizations and consumers choosing between two different software solutions could take security into account when they make their decision.
Every software user should be able to see letter grades (A, B, C, D, F) for their applications and open source libraries in real time, along with notifications when those scores change. The same system should provide actionable information to developers on the best way to improve an application's overall score. This would provide a unified platform of tools that ensures security across the entire software development life cycle — during build, test, and run.
Software Scoring: Enabling Informed Decision-Making
A software scoring system would improve national security by enabling organizations, such as the federal agencies recently victimized by the SolarWinds attack, to make informed decisions. It will also light a fire underneath software producers to take the needed steps to make their products secure.
About the Author(s)
You May Also Like
Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




