As election season ramps up, organizations engaged in the process must strengthen security to prevent chaos and disorder from carrying the day. Here's how.
As we approach November, the digital election infrastructure finds itself in the crosshairs of a new peril. Authoritarian forces and other adversaries have weaponized the fifth domain of warfare — cyberspace — against the very fabric of democracy. As the election process ramps up, organizations engaged in the political process must strengthen cybersecurity to prevent chaos and disorder from carrying the day. In so doing, they face unprecedented challenges.
Nation-state attackers and unscrupulous internal forces threaten the integrity of the electrical process, the faith of the voters in the best form of government yet devised by mankind, and even the sense of fraternity or unity among the people themselves. Cybercriminals — having already pivoted to take advantage of confusion and disruption from the pandemic — are now poised to exploit yet more opportunities.

Read more about defending the digital election infrastructure.
We've had many warning signs in the form of the bots and trolls disseminating fake news in 2016 along with the breach of the Democratic National Committee email system. More recently, we've seen activists using the TikTok service to disrupted a Trump campaign rally, hackers compromise Joe Biden's and other celebrities' Twitter accounts, and phishing attempts against state-level voter registration system personnel.
Campaigns, Government Agencies, and Election Vendors in the Crosshairs
Although we're far from full online voting, many other aspects of the political process are going digital. A bewildering number of organizations are getting information out to voters, campaigning for votes, managing the election process and collecting or counting results. As a result, the two key questions we now have to ask ourselves are: What are we trying to protect in the election process, and what is the "critical infrastructure" for an election? Per Figure 1 (above), here are the players in the digital election infrastructure:
National or state-level government agencies that manage registration, voting, and all other election processes
Campaign organizations or political action committees through which people and businesses contend for their political agendas
Media and social media through which campaign organizations influence voter opinion and citizens gather or share information
Companies providing software or services (such as registration databases, call centers, websites, and applications) to such agencies, campaigns, and media organizations
Each of these organization types requires a security program. During COVID-19 lockdowns, reopenings and second waves, all have faced accelerated digital transformation. During crises, IT and security teams tend to cut corners. For example, the so-called Twitter cryptocurrency hack may have been facilitated by a work-from-home program that weakened administrative account recovery controls.
Now that the excitement of the political season begins, it may feel like accountability for security is suspended. But that is a dangerous illusion that could be spectacularly shattered in the next breach, and we cannot afford more serious breaches against democracy itself.
Protecting the Digital Election Infrastructure
Digital election infrastructure organizations aren't one-size-fits-all. They vary in scale from the massive federal Department of Justice, to the merely large California Department of Motor Vehicles, to tiny voting technology startups. Yet all those and similar organizations play important roles. Also, the composition and culture of a government agency is vastly different from that of a software vendor, let alone a campaign run mostly by volunteers and consultants.
But all organizations must ensure one thing: leadership accountability for information risk. Any significant risks incurred should be "calculated risks" with cybersecurity programs and capabilities calibrated to them. Thus, Figure 1 doesn't stop with "basic security hygiene" in the defensive domain of the cybersecurity leadership. It adds a requirement for "rational cybersecurity programs."
Per my new book Rational Cybersecurity for Business, "lack of cybersecurity-business alignment has a corrosive effect on any security project it touches." For example, I know of a company desperate to solve a web visitor conversion rate problem that could easily afflict political campaigns. Oblivious of privacy regulations, a corporate executive sent all the weblogs (with real IP addresses) to a trial account at an analytics company in the cloud. Overnight, the executive became a hero for being able to flag returning users. But the process could have created serious regulatory trouble. Had anyone asked security, test data anonymization could have mitigated the risk of breach.
Don't Cut Corners on Security and Risk Management
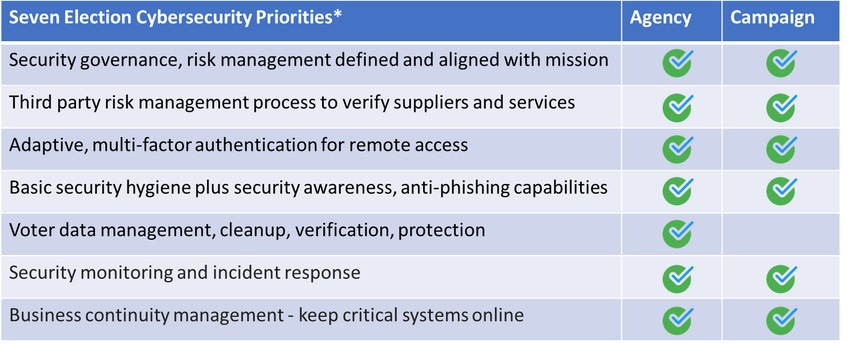
Why? Because they set the context for everything else. It is especially important for a fluid organization like a campaign to define security policies, sensitive information handling rules, access controls and incident management. The keys to rational cybersecurity programs adapted to election concerns for both agencies and campaigns include the priorities below. However, although priorities are similar for agencies and campaigns, specific controls or activities can differ considerably with agencies tending to have many older premises-based systems requiring extra-diligent vulnerability and configuration management for basic security hygiene.
Getting Out the (Mail-in) Vote
In the state and local government agency world, cybersecurity leaders must align with all business processes that manage voting and voter registration. This can be done by engaging process planning, operations, and change management personnel. Also, consult business, IT, and security staff with experience in the seven election cybersecurity priorities from Figure 2. For example, most states have undertaken identity management projects and have expertise that could be applied to processing citizen data for an election.
Zero Trust and Partisan Politics
To better counter digital risks, political campaigns should adopt the zero-trust model in every context. This starts with not trusting campaign executives to make security-related decisions without security leadership input. Nor should campaigns blindly trust vendors and cloud services. Instead, they should institute third-party risk management processes to vet the providers. Campaigns should also consider zero-trust strategies for remote access and authentication. Acquiring adaptive or multifactor authentication capabilities will enable campaigns to work more securely with a shifting array of local affiliates, consultants, and volunteers. At the same time, CISOs and other cybersecurity leaders can actively engage with campaign or government agency leaders to realign cybersecurity strategies for the election by doing the following:
Stepping up security awareness communications
Identifying election risks and opportunities to create a sense of urgency
Looking for support from key influencers in the executive ranks
Developing and selling a cybersecurity vision and strategy
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




