Kaspersky Labs sent out a warning this week that multiple phishing campaigns have targeted more than 100 universities and schools over the past year, including the University of Washington, Cornell University and others.

Over the past year, multiple phishing campaigns have targeted major universities and schools in over 100 different countries, including several US-based institutions, with threat actors looking to steal research and other intellectual property or to gather more credentials for future attacks.
The schools targeted by these phishing attacks include the University of Washington, Cornell University, Harvard Business School, Stanford University and the University of Iowa. All told, 131 universities in 16 countries were subject to these malicious campaigns.
For the last 12 months, Kaspersky Lab has been tracking these attacks, and warning schools and universities about ongoing phishing campaigns. The company published its findings in a October 24 blog post, and noted that none of the schools sustained a data breach but that these incidents are continuing.
In an email to Security Now, Nadezhda Demidova, security researcher at Kaspersky Lab and the author of the report, wrote that while these various phishing campaigns could be the work of the same group, researchers do not have proof that these attacks are coordinated.
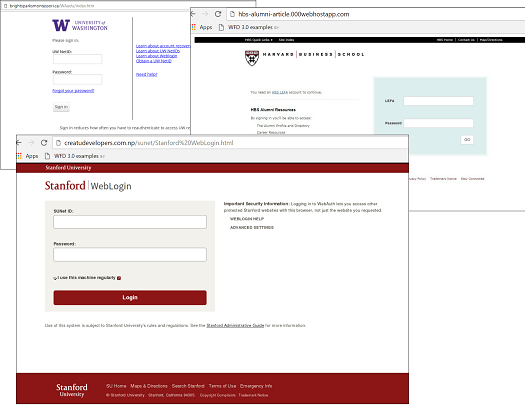
Example of fake university websites used in phishing campaigns
\r\n(Source: Kaspersky)\r\n
However, what Kaspersky found was that these attacks are designed to steal research, as well as credentials and other data, such as the IP address of the victim's device.
"Our assumption is that the main goal of these attacks was to gain access to research," Demidova wrote. "However, scammers are interested in any personal information, as they can sell it or use in the future to create spear-phishing attacks aimed at a specific person or organization."
In its blog post, Kaspersky research describes similar techniques used in these different campaigns. In most cases, the attackers created a fake webpage that was made to look like the university's official site or an intranet portal associated with the school. These pages contained a few letters that were different from the official URL.
The sites were spread to students and staff through various social engineering techniques and any data or credentials entered into these phony site were sent to the attackers, Demidova added:
"Phishing attacks have long spread not only through email, but through any available means. Since attacks are recorded regularly around the world, the methods of distribution can be completely different. The main purpose of the scammers in this case is to lure the victim to a fake website and encourage them to enter their account login data."
Overall, Kaspersky detected nearly 1,000 phishing attacks in 12 months, with 83 different campaigns targeting US-based schools and another 21 aimed at UK universities. Attacks were also recorded in Finland, Colombia, Hong Kong, India, Israel, the Netherlands, New Zealand, Poland, South Africa, Sweden, Switzerland and the UAE.
The University of Washington seemed a particularly popular target. That school accounted for over 11% of all attacks.
While phishing is one of the oldest problems in cybersecurity, these attacks have increased in scale and sophistication as of late, with Barracuda Networks and Palo Alto Network's Unit 42 describing a surge in phishing over the past year. (See Phishing Attacks Are Increasing & Gaining in Sophistication.)
In more traditional enterprises, security teams have seen an increase in Business Email Compromise (BEC) and Email Account Compromise (EAC) attacks, which use a combination of cheap hacking tools and phishing techniques to steal the credentials of company executives. (See Attackers Can Compromise Corporate Email Accounts for $150.)
For schools and universities, Kaspersky is offering some practical advice to counter these phishing attacks, including:
Always check the link address and the sender's email to determine if they are genuine before clicking. If you receive a link through email that appears suspicious, type it into the browser's address line instead of clicking through the email.
If you are not sure that a website is real and safe, never enter your credentials. If you think that you may have entered your login and password on a fake page, change your password immediately.
Avoid using the same password for several websites or services, as it puts all of your accounts at risk if your login to one site becomes compromised.
Related posts:
— Scott Ferguson is the managing editor of Light Reading and the editor of Security Now. Follow him on Twitter @sferguson_LR.
Read more about:
Security NowAbout the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




