Stolen fingerprints, fake hands, voice synthetization, and other nefarious techniques show biometrics has plenty of challenges.
August 30, 2019
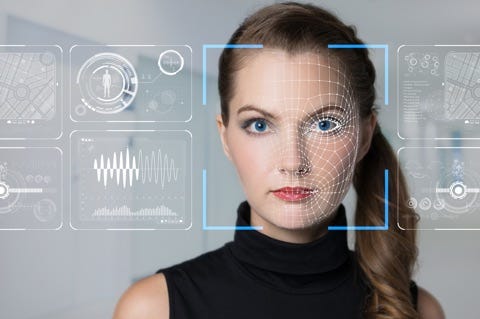
With the rise of credential stuffing and account takeovers keeping security professionals up at night, many pundits believe that biometric authentication is their answer.
But as any security veteran will tell you, there's never a simple solution. While biometrics do offer a stronger form of authentication than usernames and passwords, they come with their own risks. Several recent breaches and hacks by researchers exemplify the cracks that can show at the seams of any security model that relies too heavily on biometrics.
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




