New research shows how SMS messages manipulating vulns in insurance dongles can kill brakes on cars.
August 13, 2015
The summer of car hacks continues this week as another set of researchers demonstrated how it's possible to affect the control of a car's braking system without even engaging with any electronics embedded in the car itself. Apparently, all it really takes is just going after the Internet-connected devices that car insurance companies are increasingly using to track their customers' driving habits.
Introduced this week at the Usenix security conference in Washington, D.C., the new discovery shows that it is possible to control the braking system and other central mechanisms in cars via SMS text messaging. All this is made possible through vulnerabilities in a dongle developed by a French firm to be used by insurance companies seeking to charge insurance on a per-mile basis. Called the OBD2 dongle, the version examined by these researchers from the University of California San Diego was specifically one distributed by San Francisco-based Metromile Insurance.
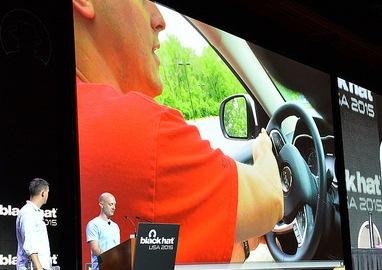
The demonstration follows closely on the heels of demonstrations at Black Hat of how attackers could kill the engine in a 2014 Jeep Cherokee from as far away as 70 miles by taking advantage of an open port in the cellular connection used by the car's infotainment system.
The new development only emphasizes the fact that cars are increasingly becoming rolling networks.
“One of the trends I am seeing in automotive system vulnerabilities is that many of these systems are using networks and protocols designed for cellular and IP networks," says Ken Westin, security analyst for Tripwire. "These tools were designed to facilitate human-to-human interaction."
As he explains, when these types of networks and protocols are repurposed for machine-to-machine interactions, they present a whole new category of threats.
"When a cell phone is compromised, there is a potential for data to be compromised, which is an inconvenience," he says. "However, when machine-to-machine communications over cellular or IP networks are compromised, it lead to a kinetic attack that could result in serious injury or even loss of life.”
But even if car manufacturers completely lock down the core systems within their own stock embedded hardware and firmware, they're creating a new networked environment that makes it possible to exploit third-party weaknesses in communications instead.
"Think twice about what you’re plugging into your car,” UCSD's Karl Koscher told Wired. “It’s hard for the regular consumer to know that their device is trustworthy or not, but it’s something they should give a moment’s thought to. Is this exposing me to more risk? Am I ok with that?”
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




