The highly-effective malware targets Middle Eastern airlines, government, financial industries and critical infrastructures with a simple but powerful backdoor created by infected Excel files attached to phishing emails.
New research released by LogRhythm Labs offers details behind the malware campaign commonly referred to as “OilRig,” including the tools, techniques, and procedures (TTPs) used to compromise security operations centers of government, financial, airline and critical infrastructure entities located primarily in the Mideast.
Unlike earlier threat intelligence reports, which addressed only a few indicators of compromise by OilRig, this new research specifies the full front-end infrastructure of the campaign, including malware associated with initial compromise (stage 1 droppers) and a significant number of indicators that have yet to be made publicly available.
Cyberattacks attributed to OilRig first surfaced in late 2015. Since then, the threat intelligence community identified two periods of high activity following the initial attack: in May and October 2016.
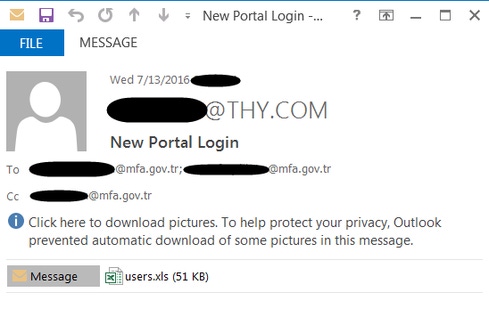
All known samples from these efforts used infected Excel files attached to phishing emails to infect victims, such as the phishing email — shown below — that appeared to be sent to an organization within the Turkish government. Once infected, the victim machine can be controlled by the attacker to perform basic remote-access Trojan-like tasks, including command execution and file upload and download.
Moving Targets
Early attacks focused on Middle Eastern banks, government entities and critical infrastructure entities. However, targets have expanded both geographically and by industry over time. For example, the October 2016 attacks targeted companies in the U.S., as well government organizations, companies and government-owned companies in Saudi Arabia, United Arab Emirates, Qatar, Turkey and Israel. OilRig also expanded its aim to include a number of Middle Eastern airlines.
History suggests this attacker is most interested in espionage, rather than other malicious activities such as theft of intellectual property. However, it is also likely that the attacker will continue to expand to other industries.

Malware Submission by Country
The origin of the malware submissions, obtained through analysis of threat intelligence data, revealed both targeted countries and those countries that are likely performing analysis on this campaign group. For example, Saudi Arabia — with 22 unique submissions — likely contains the majority of targeted organizations by this actor group. Separately, representation from Great Britain and the United States, with 11 and 9 different submissions of malware respectively, likely reflects their analysis on this campaign rather than being direct targets.
Other countries of note include United Arab Emirates, Qatar, Israel, Turkey, and Azerbaijan. While the report doesn’t fully confirm that this actor group attacked organizations from each of these countries, there are several indicators that support this conclusion. Filenames such as "TurkishAirline_Offers.xls" and "Israel Airlines.xls" make a strong correlation that these organizations were targets at one point.
Malware Submission Analysis
The LogRhythm Labs team identified 23 unique, weaponized, Microsoft Excel files that contained OilRig malware. Based on the filenames used, their country of origin, when they were identified, and the command and control method, it was determined that nearly all samples fell into one of four groups. A representative sample from each of these groups was analyzed, in detail, in the report.
When the weaponized documents are executed, most malware samples use VisualBasic for application payload to infect a system with PowerShell (.ps1) and VisualBasic scripts. The malware achieves persistence by Microsoft Scheduled Tasks, and its capabilities include very basic command execution, file upload and file download capability.
Communication Analysis
Command and control mechanisms exist for both HTTP as well as a stealthier DNS-based C2 and data infiltration/exfiltration mechanisms. The malware uses a customized UDP packet or DNS record query and response pattern for command and control and includes basic upload, download, and arbitrary command execution functionality. LogRhythm Labs’ full report outlines analysis of the methodology, and includes detection and remediation details.
While not overly sophisticated, OilRig attacks are highly effective. The attacker has created a simple, powerful backdoor using infected Excel files laced with malicious VBA, VBS, and PowerShell code. To date, the attacker has primarily used Excel files attached to spear phishing emails for malicious payload delivery. However, this attack could be easily incorporated into many different file formats that could also be attached to phishing emails.
Despite the fact that only a few industries have been targeted by this campaign, this code is widely known, which means other threat actors could incorporate it into their own campaigns and target different countries or industries. Given this, it would be wise for security analysts to guard against similar attacks regardless of their industry or location.

Related Content:
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




