PCI compliance can create headaches for companies that do online commerce. Is your e-business ready?
October 26, 2012

 Download Dark Reading's special November issue securing Web data.
Download Dark Reading's special November issue securing Web data.
Whether they're brick-and-mortar or online, merchants find the Payment Card Industry's requirements for protecting credit card data challenging and confusing.
But all retailers must understand how to protect the credit card and other customer data that comes from online transactions, because their businesses are in cybercriminals' crosshairs. Retailers are the second leading source of leaked data (after the hospitality industry), accounting for 20% of total breaches, according to Verizon's 2012 Data Breach Investigations Report. And though the U.S. Census Bureau reports that e-commerce transactions account for only about 5% of the retail economy, they've steadily grown every year.
"It's an interesting world out there, and a very scary world for a merchant, because from day one, you're a target," says John South, chief security officer for payment processor Heartland Payment Systems.
Many of the retailers playing in this scary online world are small businesses, and they're the most vulnerable: Nearly 95% of breaches happen to merchants with 100 employees or fewer, according to the Verizon report. They don't have the dedicated security and risk management teams larger businesses have.
"We aren't seeing a lot of large-scale breaches. We're seeing much smaller breaches," says Bob Russo, general manager of the PCI Security Standards Council, the governing body for PCI's Data Security Standard (PCI DSS). "These standards are right on target for the big guys with the big security departments, ... but we have to find out a way to make it easier for the smaller merchants."
Online retailers have one big security requirement that the 100% brick-and-mortar corner store doesn't have: card-not-present transactions. Because customers don't physically hand over their credit cards for online purchases, payment processors require all online merchants to submit to a quarterly network scan by an approved security vendor. Such scanning is designed to detect vulnerabilities and misconfigurations.
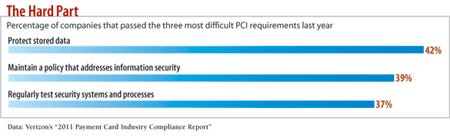
Many online retailers aren't aware of this and other PCI requirements and how to deal with them, but simple steps can make a big difference when it comes to protecting customer data. The Verizon study found that 96% of victims of successful attacks had failed to comply with the PCI rules they were subject to, and 97% of breaches could have been prevented through simple or intermediate security controls.
The following 10 steps will help your company institute the controls needed to secure cardholder data and meet PCI's requirements.
1. Know Your Infrastructure
Online merchants must worry about the degree to which their online retail systems integrate with their day-to-day business networks. Start by assessing your infrastructure to determine which systems handle transaction and cardholder data.
Network scanning and log analysis can help identify which systems have access to card data, says Greg Rosenberg, a qualified security assessor with managed security provider Trustwave. These systems are the ones that you'll want to subject to PCI DSS.
"There are a lot more attack vectors--a lot more systems--that we find and can identify vulnerabilities in than customers know about," Rosenberg says.
Get a qualified security assessor involved, he says. "I'm not looking for who can get me through my audit really quickly, but who can help me understand my risk," Rosenberg says. "I would rather significantly reduce my risk posture than quickly pass PCI."
2. Find The Data
Companies save card data for three main reasons: to better handle customer service requests, to allow easy reuse of credit cards, and to handle chargebacks, according to the Ponemon Institute's 2011 PCI DSS Compliance Trends Study. "We still have way too many companies using credit card numbers as the primary identifier for their customers," says Martin McKeay, a security evangelist at Internet services company Akamai.
Whatever the reasons for hanging on to customer data, companies should hunt down every instance on their systems, whether on Web servers, in a customer service application, or on a sales associate's laptop. Discover where the data resides, who has ac- cess to it, and whether they need the information at all.
Marketing types, for instance, want to save everything, "because someday they might use the data to send someone a coupon," says PCI SSC's Russo. "If you don't need the data, don't store it."
3. Have Fewer Data-Handling Systems
All systems that have access to the transaction data or card data at rest fall under the PCI DSS, and they're an expensive part of any assessment. So it makes sense to segment off parts of the network--and the employees involved with those parts of the network--from access to card data. This approach reduces the number of systems that fall within the scope of PCI requirements, increases security, and cuts compliance costs. "Being able to chop off big chunks of your infrastructure and saying it has nothing to do with processing transactions--that's a big help," says Chris Eng, VP of Veracode, an application security company.
A key part of this approach is to log transactions without logging the credit card numbers. "Logging is absolutely essential, and people don't do enough of it," says Jerry Hoff, VP of static-code analysis at WhiteHat Security, a Web application security provider. "But make sure that the sensitive data itself isn't logged."
4. Get Rid Of The Data
Online merchants can outsource their processing infrastructure, letting a third party handle all payment processing details and take on much of the responsibility--if not liability--for the data. "If your store sells snowboards online, then securing credit card data isn't something that you should have to focus on," Hoff says.
Companies that don't hold onto card data tend to take security more seriously and suffer fewer breaches, says the Ponemon Institute. In a survey of 670 U.S. and multinational IT managers, it found that 85% of companies that didn't retain primary cardholder data didn't suffer a breach over a two-year period. Only 40% of companies that retained data suffered no breach in that same time period.
One piece of data that the business should never retain, although many do: the card verification value, or CVV, code. "They see it as a way to increase the likelihood that the transaction will be approved," Trustwave's Rosenberg says, "but the problem is that you aren't supposed to have that data after the transaction has cleared."
Getting rid of the data reduces the PCI burden tremendously. Rather than having to comply with all 12 requirements, you can narrow your focus to two requirements: blocking access to data (requirement nine) and maintaining a policy that addresses information security (requirement 12).
PCI Prevents Breaches
64% of PCI-compliant companies had no cardholder data breach in last two years 38% of noncompliant companies were breach free Data: Poneman Institute's "2011 PCI DSS Compliance Trends Study"
You still must check your store for compliance and fill out a self-assessment questionnaire, but the overall effort is less onerous, Heartland's South says.
Just segmenting the network and minimizing retention of card data won't make your company PCI compliant, says Evan Tegethoff, a PCI solutions architect with security services firm Accuvant. No merchant can ever eliminate the scope of PCI requirements, but it can reduce them. If a third party is handling your company's data, you're still responsible for confirming that the third party is protecting the information.
The same goes for technology. Buying a PCI-compliant data protection product won't automatically make your company PCI-compliant. "Merchants frequently think, 'Let me go buy something that's PCI-compliant, and then I'm done,'" PCI SSC's Russo says. Data security technology must be adjusted to a company's needs and monitored to ensure that it's protecting all of the right data.
5. Check Out Partners
Merchants that outsource to a service provider but retain some ability to check transactions are less likely to reduce the scope of their PCI compliance, says Troy Leach, CTO at PCI SSC. "The challenge is that there is typically some sort of access to that cardholder data," Leach says. "If there is, that brings their entire environment back into scope."
You'll also want to gather information on your partners' PCI compliance. Managed service providers handle a lot of card data, making them attractive to attackers. Third parties administered 76% of systems that were breached last year. And when a breach happens, the liability generally rests with the merchant.
Ask for documentation of a third party's PCI compliance status, including a self-assessment questionnaire. Key areas to be aware of:
>> Hosting services must comply with PCI and, in particular, have a vulnerability remediation process in place, including timely patching and updating of their server software.
>> Any payment application used as the transaction engine for a store should comply with a separate set of standards: the PCI Payment Application Data Security Standard. A compliant program needs to, among other security measures, log transactions, not store full mag-stripe data, provide secure authentication, and encrypt all communications over public networks.
>> Web application scanning vendors must qualify as PCI-compliant to be listed as compliant on the pcisecuritystandards.org site.
6. Use Secure Software
Credit card data is handled most often by software, not people, so make sure you're using secure software.
A few years ago, companies that had to comply with PCI's requirement for the development and maintenance of secure applications only had to make sure their software eliminated the Open Web Application Security Project's top 10 vulnerabilities. Those requirements became more stringent last year, when PCI SSC changed the language to include other collections of vulnerabilities, such as the SANS top 25 most dangerous software errors.
No wonder companies have trouble keeping up, says Veracode's Eng. Online companies have problems securing their sites against SQL injection and cross-site scripting, the top two threats on the SANS list, never mind the other 23 issues.
7. Protect The Web Server
The critical part of an online retailer's operation is the care and maintenance of its Web server and online store. The quarterly scan that e-commerce vendors must submit to can find security vulnerabilities. In addition, under PCI, software must be kept up to date and critical flaws patched within 30 days. That may be too long.
Merchants can use one of three strategies to protect their online stores and comply with PCI: Scan code for vulnerabilities and fix any problems as part of development; dynamically scan the website to identify and patch vulnerabilities; or use a Web application firewall to block attacks. But just having a WAF isn't enough. It must be configured correctly. "They tend to be configured very, very lenient," Eng says. "Many companies run them in a mode that never blocks a request."
Companies also must think like attackers. A cross-site scripting attack, for instance, lets an attacker inject content onto a vulnerable website to make it appear to come from that site. A cross-site scripting attack may not directly compromise a merchant's website, but attackers can use the technique to redirect customers to a lookalike site from which they can collect card data.
"If I'm a hacker and I can redirect you to a website, what prevents me from redirecting you to my bad site?" says Trustwave's Rosenberg. E-commerce vendors must find these vulnerabilities during development or a security scan and fix them. Alternatively, use a WAF to block these attacks, he says.
8. Authorized Users Only
Three PCI requirements deal with authorization. Restricting physical access to cardholder data may be the easiest one to comply with. While a brick-and-mortar store has to educate and monitor cashiers who handle credit cards every day, e-commerce employees never see an actual card. Yet an online retailer may have a harder time restricting access to card data, because so many employees have legitimate access to the systems that handle the data.
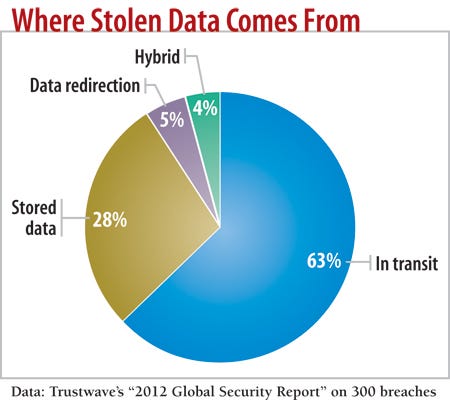
Employees and partners may also inadvertently weaken your company's data access policies by choosing poor passwords. A whopping 80% of breaches are caused by the use of weak or default administrator credentials, Trustwave said in its 2012 Global Security Report. In many cases, a third-party provider used the same password or a simple variant across many of its clients; a breach of one business led to the breach of all.
9. Encrypt, And Don't Lose The Keys
For companies that keep cardholder data, that data must be encrypted when stored and transmitted. It's all about turning cardholder data from gold data that attackers want into worthless straw that they can't access, says Mark Bower, VP of data security firm Voltage.
Techniques that encrypt transaction data and return a token, which is similar to a credit card number, to unencrypt the data are popular with merchants. By using end-to-end encryption, you cut down the number of PCI requirements and reduce the impact of breaches, because with tokenized data, even if attackers get the information, it doesn't constitute a breach, Bower says.
But encryption doesn't solve all of your problems. Many large breaches have happened because thieves were able to get the decryption key.
10. Don't Become A Check Box Culture
PCI isn't the be-all and end-all of information security. It's an "absolute bare-bones requirement," Hoff says. "It's like the sign that says 'No Running' by the pool. It doesn't mean you aren't going to have an accident."
Businesses should worry about threats beyond those covered by the PCI DSS. Attackers could use HTML injection, for example, to make Google's page-ranking bots see links in a merchant's site that aren't normally there. The result: An online retailer's site could be used to raise the page rankings of malicious websites. "You need to ask in this environment: How could I be attacked?" says Trustwave's Rosenberg.
Most important, online merchants must understand that to keep their customers, they must protect their customers' data, says Heartland's South. "Their basic obligation is that they have to protect their client's transaction. And that really has nothing to do with PCI. PCI is just a tool to get there."
More help is on the way: PCI SSC has an interest group developing guidelines for e-commerce security. Its initial report, due by December, should go a long way toward assisting all retailers in securing their customers' data.
About the Author(s)
You May Also Like
Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




