Threat uses server-side polymorphism technique to bypass antivirus software.
A massive spam wave is installing banking Trojan Dyreza on tens of thousands of computers to steal sensitive financial data from unsuspecting customers, Bitdefender malware analysts warn.
The malicious spam messages carry links to HTML files. The files link to URLs directing to highly obfuscated Javascript code that automatically downloads a zip archive from a remote location.
Interestingly enough, each downloaded archive is named differently to bypass antivirus software. This technique is called server-side polymorphism and ensures that the downloaded malicious file is always brand new.
To take the con one step further, the same Javascript code redirects the user to the localized web page of a fax service provider as soon as the archive is downloaded.
The archive content looks like regular PDF files. They are in fact executable files with a PDF icon. They act as downloaders that fetch and execute the Dyreza banker Trojan, also known as Dyre.
Dyre Malware Analysis
First seen in 2014, Dyre is similar to the infamous Zeus. It installs itself on the user’s computer and becomes active only when the user enters credentials on a specific site, usually the login page of a banking institution or financial service. Through a man-in-the-browser attack, hackers inject malicious Javascript code, which allows them to steal credentials and further manipulate accounts – all in a completely covert way.
Despite facing a threat known to resist reverse-engineering techniques, Bitdefender malware researchers have managed to analyze it and uncover the list of targeted websites. Customers of reputable financial and banking institutions from the US, UK, Ireland, Germany, Australia, Romania, and Italy have been targeted.
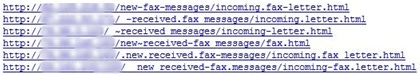
However, despite the relative sophistication of the attack, it still relies on the user’s curiosity to look into the archive and manually run its contents. A bit of caution can reduce the chances of infection. Here’s what several malicious links look like:
According to Bitdefender Labs, 30,000 malicious emails were sent in one day from spam servers in the US, Russia, Turkey, France, Canada, and the UK. Curiously, the campaign’s name – 2201us – seems to indicate the attack date (22nd January) and the targeted country (US), Bitdefender malware researchers found.
Bitdefender detects and blocks all elements of the threat: the .js file, the downloader, and the executable. The Trojan is detected as Gen:Trojan.Heur.AuW@Izubv1ni. Bitdefender reminds users to avoid clicking links in emails from unknown email addresses and, of course, to keep their anti-malware solution up-to-date with the latest virus definitions.
This article is based on spam samples provided courtesy of Bitdefender Spam Researcher Adrian Miron and technical information provided by Bitdefender Virus Analysts Doina Cosovan, Octavian Minea, and Alexandru Maximciuc.
About the Author(s)
You May Also Like
Defending Against Today's Threat Landscape with MDR
April 18, 2024The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




