In the brave new world of digital risk management, a CISO would report up to a DRO who manages risk from a business perspective and works with peers in business ops, compliance, and IT security.
The business processes in the enterprise and in government organizations have become "digital" at an accelerated pace in the past few years. In most industries, many functions that were conducted on premises or were paper-based are now being performed online via digital processes. While this trend has led to a dramatic improvement in productivity, it has also led to a new set of risk factors that extend beyond the familiar threats to traditional IT systems.
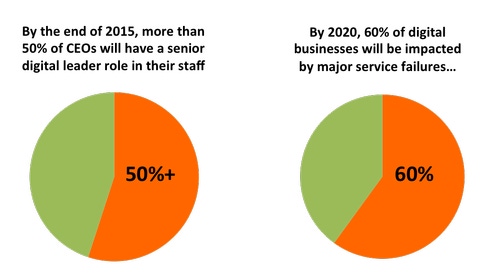
Gartner sees digital risk management (DRM) as the next evolution in enterprise risk and security, with digital risk officers (DROs) leading the charge. "By 2019, the new digital risk concept will become the default approach for technology risk management," predicted Paul Proctor, vice president and distinguished analyst at Gartner, at the firm’s 2014 Security & Risk Management Summit. He described the function of the DRO as “a mix of business acumen and understanding with sufficient technical knowledge to assess and make recommendations for appropriately addressing digital business risk."
At the Digital Risk Management Institute we agree with that prediction. In our view, the ultimate goal for DRM is to build “digital resiliency” into an organization's systems and operations in that they are designed from the ground up to detect threats and respond to events that minimize business disruption and financial losses.
DRO & CISO
In this new order, the DRO would report to a senior executive in a line of business, the COO or the chief risk officer. This role will be very different from the role of a chief information security officer (CISO). The DRO will manage risk from a business perspective and will directly work with his peers in business operations, compliance, and IT security. It is possible that in many companies the CISO and the head of physical security will start reporting to the DRO.
While many CISOs might want to evolve into the role of DRO, they would have to grow in a few dimensions to get considered for the job. They’d have to understand their company's business function and develop some level of business expertise in order to speak the language of business executives, articulate digital risk factors in operational and financial terms, and provide recommendations on risk mitigation initiatives. In doing so, they would need to be keenly aware of their role in developing a new risk management culture across functional silos and start forming partnerships with a new set of functional leaders within the line-of-business including sales, marketing, operations, and legal.
Bridging the business and IT gap
The cultural gap between business executives and IT leaders presents a real challenge for many security departments. Business executives for too long have believed that technology-related risk is a technical problem and have delegated it to technical people operating in IT, separate from the business. Technical people don't understand their organization's business function well and don't know how to articulate risk in financial and operational terms. This has led to situations where business executives don't understand the problem and where technical people blame executives for insufficient attention and funding of their security initiatives.
One step towards resolving this cultural divide would be through the empowerment of a DRO with a mandate to build the organizational processes and best practices necessary to measure and manage digital business risk, including mapping of important business processes, assessment of exposure to threats, quantification of business, and prioritization of risk mitigation initiatives. Building a DRM program will be complex, but a worthwhile investment for companies that want to achieve the right balance between protecting the organization and running the business.
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




