Security operations capabilities for the masses is long overdue. Here’s how to find a solution that meets your budget and resources.
The security operations platform is quickly emerging as a favorite talking point for 2017, even for organizations that do not find themselves with an expansive budget to improve their security maturity and posture. Of course, doing so is a complex undertaking with a wide variety of moving parts. Or is it?
Historically, advanced SecOps has been beyond the reach and resources for all but the most elite organizations. Today, the cloud has opened up new possibilities for these enhanced capabilities at reduced cost. This, in turn, creates new opportunities for mid-sized and smaller enterprise-sized organizations.
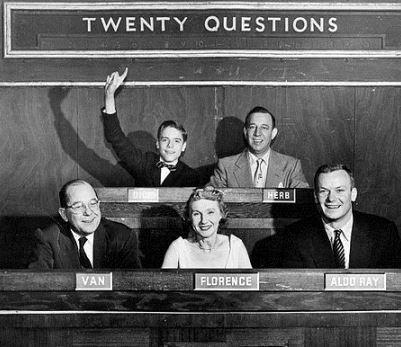
Of course, where there is interest, there are vendors ready to pounce. Lately, there are quite a few vendors talking about their security operations platforms. How can the conscientious security buyer interrogate potential vendors to make the most-informed decision? As you might guess, I would suggest a game of 20 questions.
1. How do you make it easy to seamlessly operationalize intelligence? Reliable, high-fidelity intelligence is an important component of a mature security operations capability. Plenty of vendors offer intelligence, and I have already discussed how to differentiate between different intelligence offerings. But there is another important point worth mentioning here. The greatest intelligence in the world won’t help an organization if it can’t operationalize it. In other words, if it isn’t easy for you to leverage intelligence to help defend your organization, it is more or less useless.
2. How do you facilitate risk mitigation? Everyone knows that security is all about risk mitigation. But if knowledge about risks and threats to the organization cannot be operationalized to help manage and mitigate risk, that knowledge is wasted.
3. Do you honestly believe that I want more alerts? I am suffering from a bad case of alert fatigue. What I need is help making order out of the chaos, and turning all of that information into knowledge.
4. Where is my context? Alerts without the appropriate context do not provide a true understanding of what is going on. That makes it difficult for organizations to make educated, informed decisions. Context is king.
5. Can you provide me protection against a variety of attack vectors that compromise organizations? If a security operations platform cannot cover multiple different attack vectors, it isn’t going to cut it.
6. Can you help me see? The importance of proper visibility across the network, endpoints, mobile, cloud, and SaaS is huge. If you can’t see it, you can’t detect it.
7. How do you model attacker behavior? The best way to identify attacker behavior within an organization is to deeply understand different characteristics of that behavior, model them, and subsequently develop algorithms that recognize them. Simply developing algorithms without understanding how attackers attack isn’t going to be very productive.
8. How is your performance? Security operations is about both collection and analysis. It isn’t enough to collect vast quantities of data. Any reasonable SecOps platform needs to be able to allow analysts to interrogate that data rapidly.
9. Do you have integrated case management? The “swivel chair” effect, and the days of cutting and pasting manually between different systems needs to come to an end. If the analysis and investigation I am doing cannot be fed automatically into a case or ticket, that isn’t going to work for me.
10. How do you scale? I want to know that as my needs grow, I can buy additional capacity and functionality as necessary without a long, complex, and disruptive deployment cycle.
11. How do you provide integration between distinct components in a diverse security ecosystem? My security ecosystem is diverse, and you need to be able to help me maximize and optimize my existing investments.
12. How flexible is your query language? Can I ask precise, incisive, targeted questions? If your query language does not support that, it is not helpful.
13. Can you augment my existing talent? Although I want to run security operations 24x7, that’s not a realistic expectation, given my current resources. How can you augment my staff to help us get there?
14. Do you provide seamless pivoting across a wide variety of data sources? I don’t have time to issue multiple queries across multiple different systems to get the relevant data that I need. If you can’t provide me a single interface to all of the data across my security ecosystem, I’m not interested.
15. Do you have an integrated automation and orchestration capability? Manual processes are inefficient and error-prone. I need to take advantage of automation and orchestration, but it needs to be integrated into the platform for that platform to be realistic.
16. Will you end my cutting and pasting nightmare? In 2017, seamless integration between alerting, analysis, investigation, case management, and documentation should be a given.
17. Can you help me free up resources for higher order work? It is not a good use of time or money to have analysts spending most of their time performing clerical tasks. I need them to focus on higher-order work.
 More on Security
More on Security
Live at Interop ITX
18. Do you have real analytics based on real knowledge of attacker behavior? Everyone talks about analytics these days. But the only analytics that stand a chance of reliably detecting attacker behavior with low noise are analytics based on intimate knowledge of attacker behavior.
19. Do you support flexible deployment options? Any realistic platform needs to be easily consumable in a variety of different ways.
20. Is your solution affordable? The time to bring security operations to the masses is long overdue. In order to make that a reality, any solution needs to suit my budget.
Related Content:
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




