Secret "supply-chain interdiction" program intercepts networking equipment being shipped overseas and adds phone-home surveillance capabilities, says Guardian report.
The National Security Agency has routinely intercepted networking equipment that's built in the United States, added backdoor access capabilities, then shipped the devices to their intended recipients abroad.
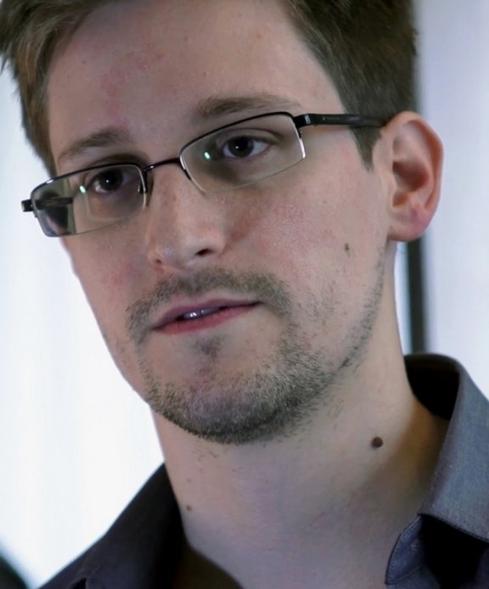
So says a report by journalist Glenn Greenwald published Tuesday by the Guardian. Greenwald cites a June 2010 document (leaked by former NSA contractor Edward Snowden) labeled as being from the head of the NSA's Access and Target Development group.
"The NSA routinely receives -- or intercepts -- routers, servers, and other computer network devices being exported from the US before they are delivered to the international customers," Greenwald writes. "The agency then implants backdoor surveillance tools, repackages the devices with a factory seal and sends them on. The NSA thus gains access to entire networks and all their users."
According to the document from the NSA -- the US intelligence agency charged with practicing signals intelligence -- this supply chain "SIGINT tradecraft... is very hands-on (literally!)."
When the hacked networking equipment is brought online, it phones home to NSA-controlled servers. "In one recent case, after several months a beacon implanted through supply-chain interdiction called back to the NSA covert infrastructure," Greenwald quotes the leaked NSA report. "This call back provided us access to further exploit the device and survey the network."
Greenwald has worked with filmmaker Laura Poitras to publish the lion's share of the files leaked to date by Snowden, and his NSA router-backdoor report was timed to coincide with Tuesday's publication of his book, No Place to Hide: Edward Snowden, the NSA, and the U.S. Surveillance State.
The report has already triggered a flood of related questions, including the degree to which technology manufacturers and shipping firms might be colluding -- or are legally forced to comply -- with the NSA's equipment-interception program.
But it's unclear how often the technique gets used. Last year, Snowden told Hong Kong's South China Morning Post that for eavesdropping, the NSA prefers to hack into infrastructure on a grander scale. "We hack network backbones -- like huge Internet routers, basically -- that give us access to the communications of hundreds of thousands of computers without having to hack every single one," he told the Post.
Last year, however, security expert Bruce Schneier -- who also has access to the trove of NSA documents leaked by Snowden -- warned that the NSA was hacking networking equipment as well. "The NSA also attacks network devices directly: routers, switches, firewalls, etc.," he said. "Most of these devices have surveillance capabilities already built in; the trick is to surreptitiously turn them on."
The revelations over the NSA's backdoor-installation program cast new light on warnings issued last year by former CIA director Michael Hayden, who accused Chinese telecom equipment maker Huawei of actively spying for the Chinese government. Expect the latest NSA leak to stoke the ongoing debate about the agency's tactics, and their impact on the privacy rights of non-US citizens.
But some information security experts have warned that the NSA's programs -- and bigger surveillance-state analyses -- must be kept in context. "This is the problem with Greenwald: his inept analysis created a whole new urban mythology about who did what to whom," says Thomas H. Ptacek, principal at Matasano Security, via Twitter.
Indeed, if there's one espionage truism, it's that whatever one side is doing, the other side is likely not far behind -- as has been proven by tit-for-tat accusations from both China and the United States that one is hacking the other.
At the same time that Hayden singled out Chinese networking manufacturers for colluding with the military, he conceded as much, confirming what the NSA leaks have made quite clear: The United States hacks foreign targets. But Hayden portrayed US efforts in different terms. "I fully admit: we steal other country's secrets. And frankly we're quite good at it," he said. "But the reason we steal these secrets is to keep our citizens free, and to keep them safe. We don't steal secrets to make our citizens rich. Yet this is exactly what the Chinese do."
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




