Serverless forces software architects and developers to approach security by building it in rather than bolting it on. But there is a downside.
One of the biggest security upsides to developing on serverless architectures is that organizations don't have to deal with the daunting task of having to constantly apply security patches for the underlying operating system. These tasks are now in the domain of the serverless architecture provider.
Yet even though developers are no longer accountable for the many security tasks now handled by the serverless cloud provider, they are still responsible for designing robust applications and making sure that application code doesn't introduce application layer vulnerabilities. It seems that this responsibility is not going away any time soon.
Moreover, any configuration related to the application itself or to the cloud services it interacts with would still need to be secure; again, this is still the responsibility of the application owner.
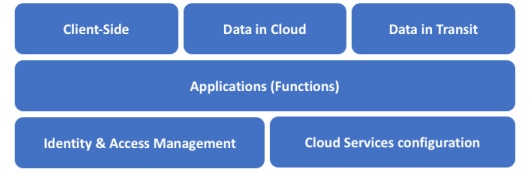
In the serverless world, the cloud vendor and you share security responsibilities. The following images demonstrate the shared serverless security responsibilities model:
While serverless architectures introduce simplicity and elegance, it also introduces a new set of issues and application security challenges:
Increased attack surface: Serverless functions consume data from a wide range of event sources such as HTTP APIs, message queues, cloud storage, and Internet of Things device communications. This increases the attack surface dramatically, especially when messages use protocols and complex message structures, many of which cannot be inspected by standard application layer protections such as Web application firewalls.
Attack surface complexity: The attack surface in serverless architectures can be difficult for some to understand given that such architectures are still rather new. Many software developers and architects have yet to gain enough experience with the security risks and appropriate security protections required to secure such applications.
Overall system complexity: Visualizing and monitoring serverless architectures is still more complex than standard software environments
Inadequate security testing: Performing security testing for serverless architectures is more complex than testing standard applications, especially when such applications interact with remote third-party services or with back-end cloud services such as NoSQL databases, cloud storage, or stream processing services. In addition, automated scanning tools are currently not adapted to scanning serverless applications.
Traditional security protections become unsuitable: Since organizations that use serverless architectures do not have access to the physical (or virtual) server or its operating system, they are not at liberty to deploy traditional security layers such as endpoint protection, host-based intrusion prevention, Web application firewalls, or RASP (runtime application self-protection) solutions.
This last point mandates a drastic paradigm shift in application security for serverless architectures. By definition, in a serverless architecture you only control your application's code, and that's pretty much the only thing you own. This means that if you need to protect your own serverless code, your only option is to make sure that you write secure code and that you bake security into your application.
That's actually not a bad thing — serverless computing forces software architects and developers to approach security the way it should've been approached early on — by building security in rather than bolting it on.
Related Content:

Join Dark Reading LIVE for two cybersecurity summits at Interop ITX. Learn from the industry’s most knowledgeable IT security experts. Check out the security track here. Register with Promo Code DR200 and save $200.
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




