New entrants to the top 25 show that bad password creators are fans of sports, superheroes, dragons, and NSFW numeral combos.
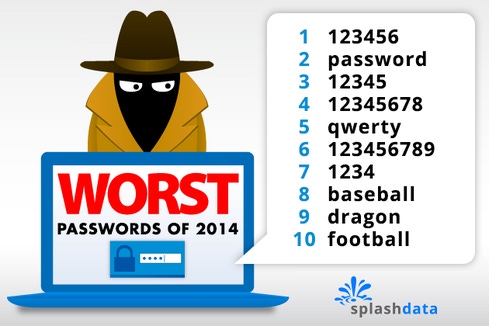
"123456" and "password" continue to be the two most common passwords found on the Internet, thus reining SplashData's annual "Worst Password List" for the fourth year in a row. New entrants to the top 25 this year show that bad password creators are fans of sports, superheroes, dragons, and not-safe-for-work numeral combinations.
{image 1}
This is the fourth year SplashData has identified the most popular passwords by compiling sets of credentials leaked online. This year's study looked at more than 3.3 million leaked passwords, mostly from users in North America and Western Europe.
"The bad news from my research is that this year's most commonly used passwords are pretty consistent with prior years,” said Mark Burnett, author of “Perfect Passwords,” who worked with SplashData on this year's study.
“The good news," says Burnett, "is that it appears that more people are moving away from using these passwords. In 2014, the top 25 passwords represented about 2.2% of passwords exposed. While still frightening, that's the lowest percentage of people using the most common passwords I have seen in recent studies."
Nine of the top twenty-five most common passwords were all numerals, and fourteen of them were all lowercase letters. The other two were a combination of lowercase letters and numerals ("abc123" and "trustno1").
Not a single capital letter or special character made the cut. Most of the common passwords were no more than six characters long. Nine of the top 25 choices were simply dictionary words. All this shows that few places are enforcing any kind of strong password policy.
New to the top 25 were "baseball" and "football." Other lowercase sports and sports teams were found in the top 100. For the more whimsical security-unsavvy users, "dragon," "superman," and "batman" jumped into the top 25 also.
In addition to "password," which ranked second, users were fond of "letmein," "trustno1," and "access," which is new to the list.
No swear words made it into the top 25, but SplashData says they remain popular. The password "iloveyou," which was in the top 25 last year, has fallen off the list entirely, "696969" has taken its place.
About the Author(s)
You May Also Like
Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




